In recent years, malicious actors have started attacking industrial control systems and key sectors of nations’ critical infrastructure to inflict damage that transcends the cyber world and traditional IT assets. The risk to public safety cannot be overstated, as these types of cyber attacks have real-world potential to inflict harm on humans. These “industrial control systems” that control the many facets of our nation’s critical infrastructure are more commonly known as operational technology (OT) devices. The same goes for IoT devices and industrial internet of things (IIoT) devices. IoT is the network of physical objects that contain embedded technology to communicate, sense, or interact with the internal or external state of its environment. The public and private sectors have many OT and IoT devices in industries such as defense, power generation, robotics, chemical, and pharmaceutical production, oil production, transportation, and mining—
Alarmingly, in 2021 there were two incidents of local water treatment plants in the US being a target of cyber attacks. One cyber attack occurred in the San Francisco Bay area in January 20212 and another occurred in February 2021 in Oldsmar, Florida.3 In the Oldsmar, Florida cyber attack, the malicious actors attempted to increase the amount of sodium hydroxide in the water supply to potentially dangerous levels. Thankfully, the attack was thwarted by a plant supervisor who caught the act in real-time and reverted the changes. These cyber attacks occurred on OT devices used for critical infrastructure at a local level, but similar cyberattacks are playing out in the real world on a national level as well.
On May 7, 2021, Colonial Pipeline, an American oil pipeline system responsible for 45 percent of all fuel consumed on the US East Coast, suffered a ransomware cyber attack that crippled all pipeline operations for about six days.4 The aftermath of this attack caused fuel shortages in six US states as well as the US capital, Washington D.C.
These cyberattacks on OT devices may not be new, but they underscore how dangerous the threat is to our critical infrastructure, as well as how great the risk is to our overall public safety.
The US government has taken notice of the increased threat against OT systems and has responded accordingly. Per the President’s Executive Order on Improving the Nation’s Cybersecurity issued on May 12, 2021, “The Federal Government must bring to bear the full scope of its authorities and resources to protect and secure its computer systems, whether they are cloud-based, on-premises, or hybrid.5 The scope of protection and security must include systems that process data (information technology (IT)) and those that run the vital machinery that ensures our safety (operational technology (OT)).” The Quzara CybertorchTM solution, in conjunction with Microsoft Defender for IoT and Microsoft Sentinel, helps agencies meet compliance with various aspects of this executive order. This includes providing agencies with a means to monitor IT and OT operations and alerts, to respond to attempted and actual cyber incidents, to facilitate logging, log retention, and log management.
With the threat of cyber attacks impacting OT and IoT devices on the rise, it is important now more than ever for national, state, local governments, and their private sector partners to be vigilant in securing their OT and IoT devices that operate or assist critical infrastructure.
The current state of cybersecurity in OT and IoT environments
While it is encouraging that the US Government is giving greater emphasis to secure OT and IoT infrastructure, they and private corporations with OT and IoT devices face an uphill battle. This is because many OT and IoT environments use outdated (and therefore, unsecure) operating systems and software. A comprehensive report from CyberX (acquired by Microsoft) in June 2020 titled Global IoT and ICS Risk Report was compiled based on data gathered from 1,821 production OT and IoT networks using passive, agentless monitoring with patented deep packet inspection (DPI) and network traffic analysis (NTA) algorithms. These production networks spanned diverse IoT and ICS systems—
- 71 percent had outdated or unsupported operating systems.
- 64 percent had unencrypted passwords.
- 54 percent were remotely accessible.
- 22 percent had indicators of threats.
- 27 percent had direct internet connections.
- 66 percent had no automatic updates.
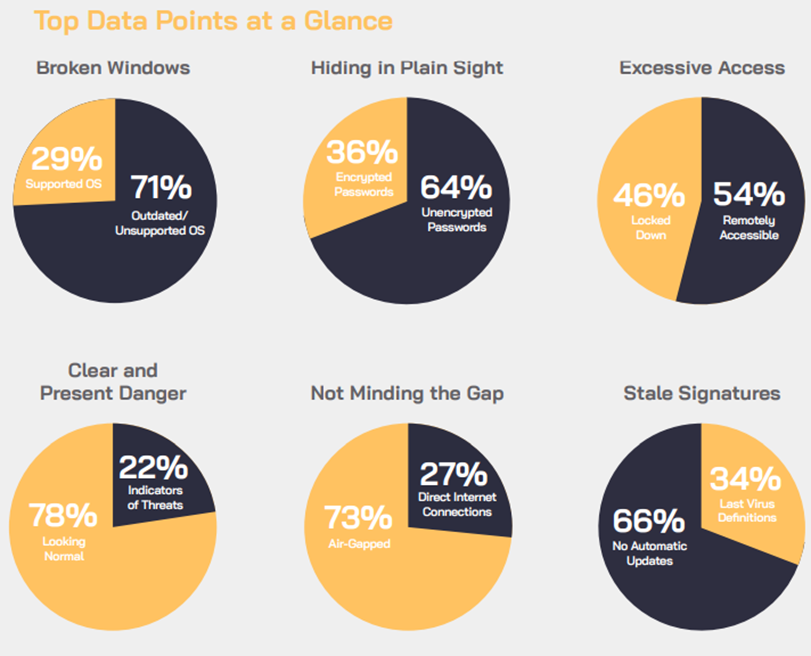 Figure 1. CyberX report high-level findings.
Figure 1. CyberX report high-level findings.
Securing and monitoring OT and IoT devices
It is critical for national, state, local governments, and their private sector partners to secure their OT and IoT environments from cyber attacks—
Automated asset inventory
Microsoft Defender for IoT is an agent-less solution that—
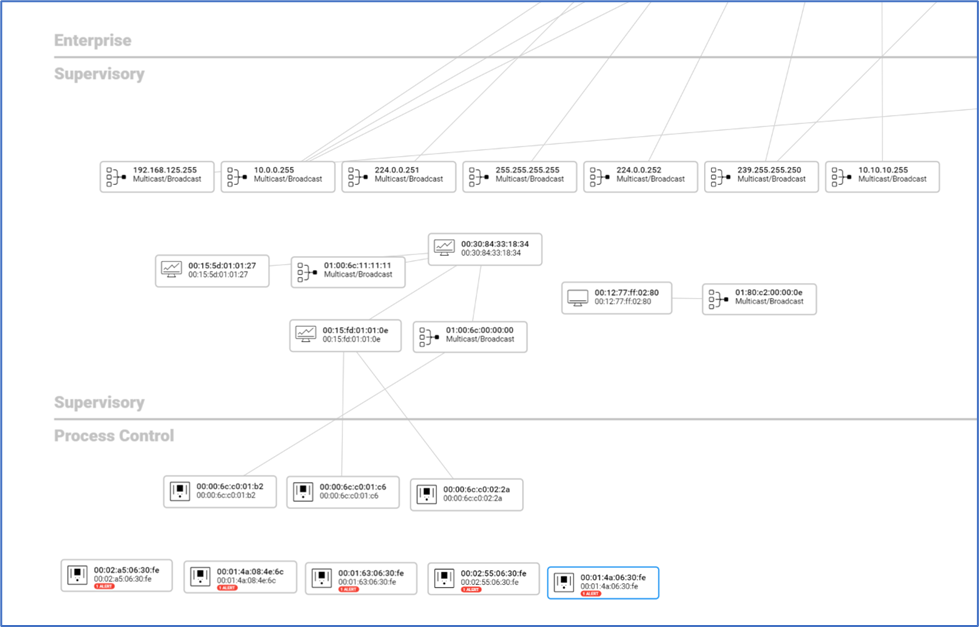 Figure 2. Auto-generated Asset Inventory Map in Purdue model layout.
Figure 2. Auto-generated Asset Inventory Map in Purdue model layout.
By identifying which assets communicate with each other in a Purdue model format, valuable information is gathered that depicts which machines can communicate out to the internet from the OT network. These internet-connected machines are the ones we prioritize locking down and monitor more closely for suspicious traffic. Identifying internet-connected assets is just one example of what the asset inventory map can display. The asset inventory map also reveals any shadow devices that are on the OT and IoT network. In other words, by revealing all assets on the OT network, the asset inventory map will identify any IT, OT, and IoT devices that the IT department may not be officially aware of. Furthermore, the asset inventory map helps IT security teams identify “single points of failure” in their environment based on the network topology and architecture. Quzara CybertorchTM encourages hardening these assets that are “single points of failure” and creating redundancy to ensure operations aren’t disrupted if these assets were to ever go down unexpectedly.
Vulnerability management of OT and IoT devices
Quzara CybertorchTM can identify known vulnerabilities on OT and IoT devices by leveraging Microsoft Defender for IoT. Microsoft Defender for IoT proactively identifies vulnerabilities such as unpatched devices, unauthorized Internet connections, and subnet connections. Beyond identifying vulnerabilities, Microsoft Defender for IoT also identifies changes to device configurations, programmable logic controller (PLC) code, and firmware. Quzara CybertorchTM consolidates all this information and generates executive summary reports listing out all the vulnerabilities for all OT and IoT devices in a network—
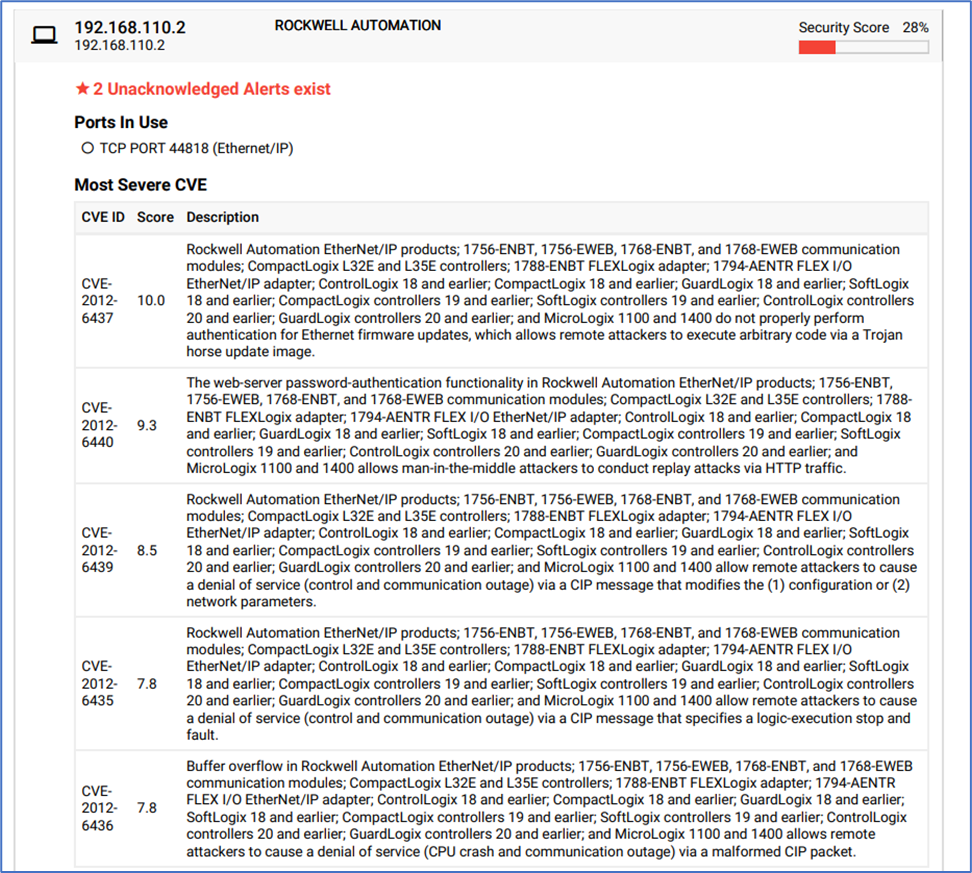
Figure 3. Vulnerabilities present on an OT workstation.
Continuous monitoring for OT and IoT devices
Quzara CybertorchTM is a security operations center as a service (SOC-aaS)that leverages Microsoft Sentinel to continuously monitor IT environments as well as OT and IoT environments. Microsoft Sentinel is a security information and event management (SIEM) tool with security orchestration, automation, and response (SOAR) capabilities. Microsoft Sentinel has native interoperability with Microsoft Defender for IoT and is cloud native. Using Microsoft Sentinel, Quzara CybertorchTM can ingest logs from IT, OT, and IoT devices, creating a unified bird’s-eye view across IT and OT boundaries and empowering our security operations center (SOC) analysts to then analyze for signs of malicious activity.
When using other products, typically a lot of work and expertise is required to create rules that aggregate disparate alerts into consolidated incidents. Quzara CybertorchTM greatly reduces the work that is required to create targeted rules for OT and IoT incidents, as Microsoft Sentinel has pre-built analytics rules for OT and IoT devices when used in conjunction with Microsoft Defender for IoT. Functionality also exists to create custom rules and playbooks from these OT and IoT alerts. This functionality empowers our SOC analysts to help detect, alert, and assist personnel in mitigating vulnerabilities on OT and IoT devices.
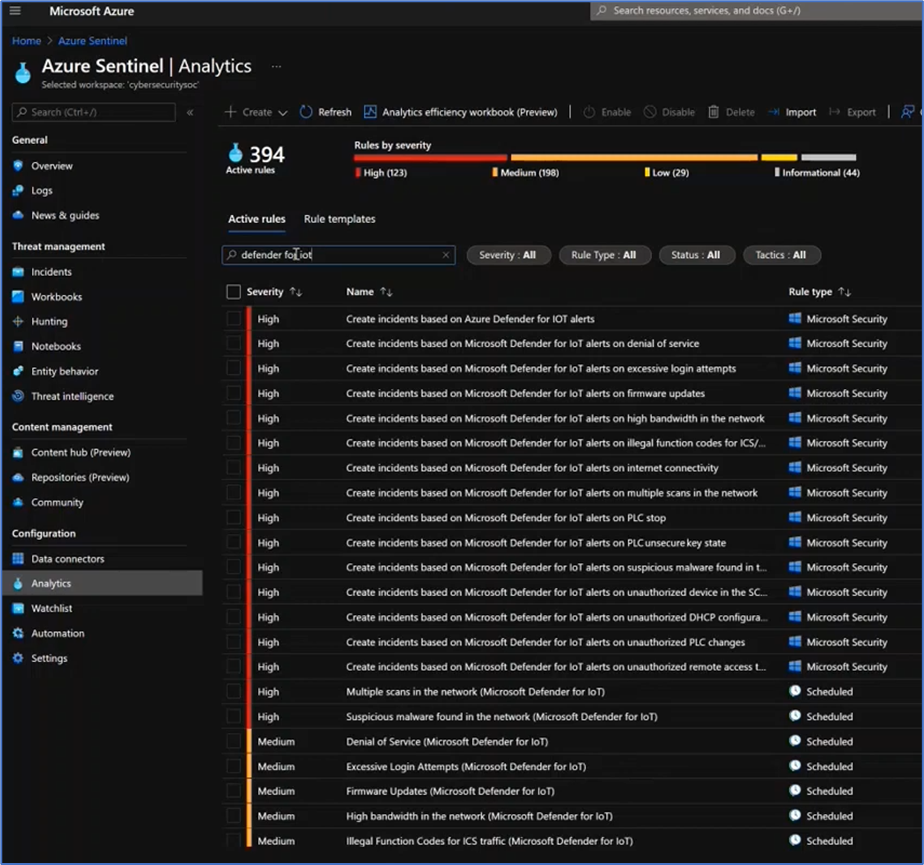 Figure 4. Microsoft Defender for IoT analytics rules in Microsoft Sentinel.
Figure 4. Microsoft Defender for IoT analytics rules in Microsoft Sentinel.
If your team, company, or clients have an OT or IoT environment and are interested in obtaining an OT or IoT cybersecurity risk assessment, please reach out to Quzara CybertorchTM or by email here.
About Quzara CybertorchTM
Quzara Cybertorch™ is a security operations center as a service (SOCaaS) and managed detection and response (MDR) purpose-built to meet the needs of U.S. Civilian, Department of Defense (DoD), and Defense Industrial Base (DIB) customers for extended detection and response (XDR), Vulnerability Management, OT and IoT monitoring, and security monitoring needs. Their security operations center as a service, vulnerability management, and XDR capabilities are based on the National Institute of Standards and Technology (NIST) 800-53 FedRAMP HIGH controls. Their entire technology stack leverages FedRAMP HIGH Authorized systems. Quzara Cybertorch’s™ team of Security Analysts are all based and operate within the US, with emphasis on security clearances and government support experience. Explore Quzara Cybertorch ™ and visit the Quzara Cybertorch ™ listing in the Microsoft commercial marketplace.
1Crimes of Opportunity: Increasing Frequency of Low Sophistication Operational Technology Compromises, Mandiant, May 25, 2021.
This article first appeared on the Microsoft Security blog, on March 3, 2022.


